Successful SQL injection attacks provide the attacker with access to the database. The attacker is able to read sensitive or private data, insert, update, delete or otherwise modify the data, perform shutdowns on the database and similar administrator operations, send commands to the operating system, or retrieve content from specific files. (2020, December 13). Highly Evasive Attacker Leverages SolarWinds Supply Chain to Compromise Multiple Global Victims With SUNBURST Backdoor. Retrieved January 4, 2021. (2020, December 18). Analyzing Solorigate, the compromised DLL file that started a sophisticated cyberattack, and how Microsoft Defender helps protect customers.

Trojan.MacOS.Dropper Description
Trojan.MacOS.Dropper is a generic name for the dropper components of trojans. The purpose of a trojan is to infect the victim's system without getting detected or raise any suspicion. Once it achieves that, there are various functions the trojan can have:
- Exfiltrate data (passwords, contacts, etc.)
- Install or enable the installation of other malware
- Record the victims activities
- Make the victim's machine a part of a botnet
- Disrupt workflow
Supply Dropper Mac Os 11
The dropper component is usually one which 'drops' the payload. The payload is usually more harmful malware that would be more difficult to get in without getting detected. Cuberot mac os.
Supply Dropper Mac Os Catalina
Trojan.MacOS.Dropper Description
Trojan.MacOS.Dropper is a generic name for the dropper components of trojans. The purpose of a trojan is to infect the victim's system without getting detected or raise any suspicion. Once it achieves that, there are various functions the trojan can have:
- Exfiltrate data (passwords, contacts, etc.)
- Install or enable the installation of other malware
- Record the victims activities
- Make the victim's machine a part of a botnet
- Disrupt workflow
Supply Dropper Mac Os 11
The dropper component is usually one which 'drops' the payload. The payload is usually more harmful malware that would be more difficult to get in without getting detected. Cuberot mac os.
Supply Dropper Mac Os Catalina
Supply Dropper Mac Os Download
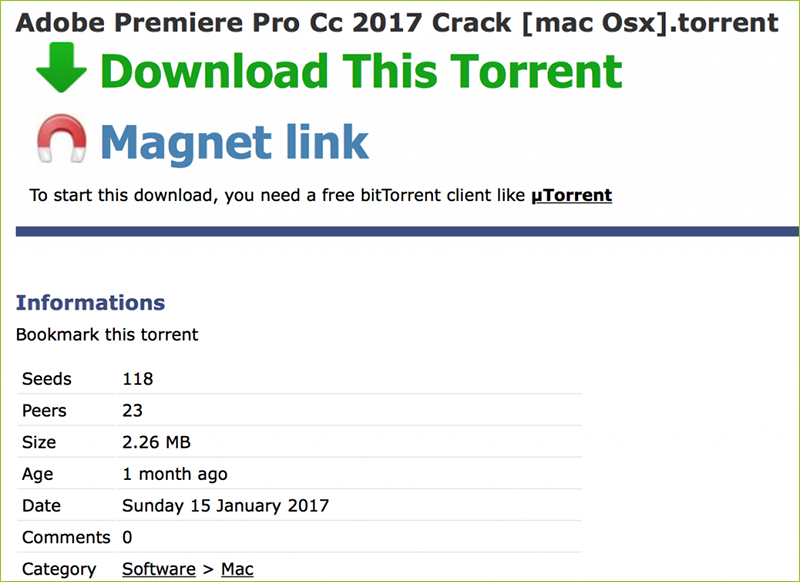
The most common ways for trojans to infect a system include spam email campaigns with malicious attachments, fake updates for already installed software, compromised websites and freeware bundles. While the manual removal of trojans can be tricky and usually requires a skilled user, reputable security solutions will easily prevent an infection or remove one after the fact.

